Smart Threat Protection & Resilient Infrastructure
Shield every endpoint with AI-driven threat detection and adaptive network control.
Risk-Based Strategy Design
Define critical vulnerabilities and build a proactive defense model. Tailor your cybersecurity framework to meet industry-specific risk tolerance and regulatory demands.
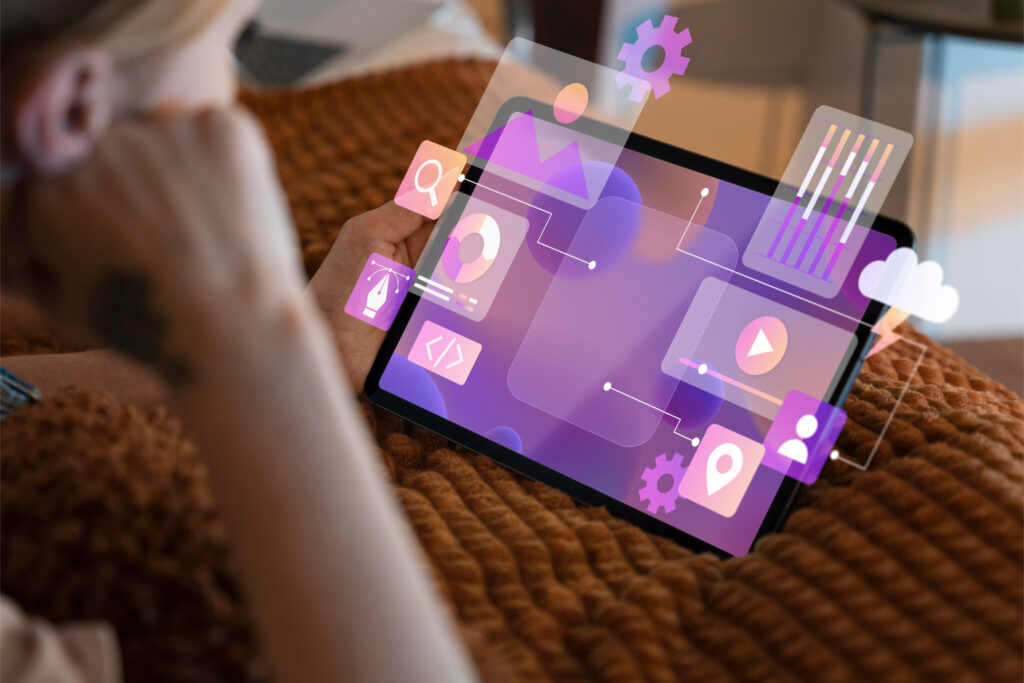
Unified Threat Monitoring
Track real-time data threats, malware attempts, and system intrusions. Use centralized dashboards powered by AI to pinpoint vulnerabilities instantly.
Compliance-First Security
Stay compliant with GDPR, ISO 27001, HIPAA, and more. Automate documentation and audits to avoid penalties and ensure trust across clients and regulators.
Zero Trust Access Control
In today’s evolving threat landscape, identity is the new perimeter. Many organizations still rely on traditional, perimeter-based security models that trust users once they’re inside the network.
In most of the cases, it’s not a sophisticated hacker breaking through firewalls, it’s someone using a legitimate username and password from an unsecured or non-compliant device.
That’s where the traditional approach fall short of as it exposes businesses to data breaches, unauthorized access, and insider threats.
At Ablyt, we help organizations transition to a Zero Trust IAM framework — where no user or device is trusted by default, and every access request is continuously verified.
Our experts integrate Identity and Access management solutions that provide:
By implementing Zero Trust IAM, Ablyt strengthens your organization’s security posture, minimizes attack surfaces, and ensures only the right people access the right resources at the right time ensuring your business data stay protected from modern cyber threats.
Single Sign-On:
With ABLYT, organizations can unlock the full potential of Single Sign-On, providing secure, one-click access to all business applications and connected devices. Users authenticate once and instantly access all authorized resources, eliminating repeated logins and password fatigue—boosting productivity from day one. ABLYT combines enterprise-grade security with seamless access, integrating Multi-Factor Authentication, adaptive risk checks, and conditional access policies. This ensures that only verified users and trusted devices can access sensitive resources, while maintaining a consistent login experience across desktops, mobile devices, cloud apps, and on-premise systems. IT teams benefit from centralized access management, enabling them to onboard users, enforce policies, and monitor access from a single dashboard. With audit logs and reporting, organizations can meet compliance requirements, quickly identify risks, and strengthen overall identity protection—all while simplifying IAM operations and improving user experience.


Centralized Identity Governance:
Managing user identities, roles, and access rights across multiple applications and devices can be complex. ABLYT helps organizations securely manage identities and access across on-premise and cloud applications from a single platform. Centralized Identity Governance helps to manage, monitor, and enforce identity policies, giving organizations full control over who can access what, when, and how. With ABLYT, organizations can define role-based access policies, enforce least-privilege access, and gain centralized visibility into user activity reducing risk, preventing policy violations, and ensuring compliance with regulatory requirements. ABLYT helps streamline IAM operations, simplify audits, and maintain secure, compliant access across all applications and devices—protecting critical resources while keeping operations efficient.
Multi-Factor Authentication:
ABLYT helps organizations in integrating the Multi-Factor Authentication solution which adds an extra layer of security beyond passwords ensuring only verified users can access apps, devices, and business data. By combining passwords with additional authentication factors, Multi-Factor Authentication protects organizations from credential theft, phishing, and unauthorized access. With intelligent, policy-driven MFA, ABLYT delivers strong security without slowing users down, supporting secure, compliant access across all applications and devices.

Continuous Monitoring :
ABLYT enables continuous verification of user access by monitoring authentication activity, access behavior, and policy compliance in real time. This ensures that trust is not assumed after login but continuously validated. By integrating IAM solutions within the organization, ABLYT helps detect anomalies early, enforce adaptive access controls, and maintain secure, compliant access across all applications and devices.
User Lifecycle Management :
ABLYT simplifies identity management across the entire user journey starting from onboarding to role changes and offboarding. By automating user provisioning and access control, ABLYT ensures the right users have the right access at the right time. Integrated with SSO and MFA, ABLYT enforces secure, role-based access across applications and devices, reduces IT overhead, and helps organizations maintain compliance with Zero Trust principles.


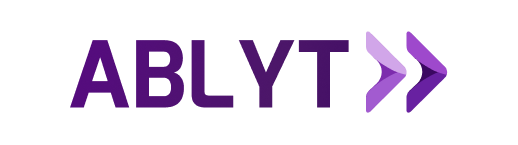
Endpoint and Device Compliance
At today’s pace of digital transformation and dispersed devices, compliance aren’t optional—they’re foundational. Ablyt puts both front and centre, equipping your organisation with the controls and visibility you need to confidently manage devices and data—anywhere, anytime.
Ablyt aligns with CIS (Center for Internet Security) Level 1 benchmarks, ensuring that every managed device adheres to globally recognized security best practices.
The IT teams can effortlessly enforce CIS-recommended configurations such as strong password policies, device encryption, secure network access, restricted admin privileges, and timely OS updates across all endpoints.
The platform provides real-time compliance monitoring, remote lock/wipe, and policy enforcement, ensuring devices remain secure and audit-ready at all times.
By automating CIS Level 1 controls through Ablyt, organizations strengthen endpoint security, reduce vulnerabilities, and maintain a consistent compliance posture across Windows, macOS, Android, and iOS devices.
Endpoint Security at Scale
Defend every device across locations and networks with scalable protection layers.
Secure Remote Access
Protect your hybrid workforce with encrypted VPN tunnels and multi-factor authentication (MFA). Enable secure login across offices, homes, and public networks.
Patch Management Automation
Apply critical updates across all systems on time. Eliminate vulnerabilities through timely patching without disrupting workflows.
Mobile Device Security
Lock down enterprise mobility with mobile device management (MDM) tools. Enforce security policies, track assets, and remotely wipe data if needed.
Rapid Response & Recovery
Bounce back quickly with breach detection, forensic insight, and auto-recovery workflows.
Incident Response Playbooks
Activate step-by-step remediation protocols. Minimize downtime and control damage with pre-configured breach response.
Backup & Restore Management
Recover business data instantly. Use automated, encrypted backups across devices and servers with scheduled recovery testing.
Intrusion Detection Systems (IDS)
Use real-time detection systems to flag unauthorized access attempts. Prevent escalation through intelligent firewall responses.
Fully Integrated Security Ecosystem
Connect your cybersecurity with enterprise-wide operations for seamless coordination and control.
SIEM Integration
Aggregate logs and threat data from all platforms. Use Security Information and Event Management (SIEM) tools to monitor, analyze, and act on threats.
Cloud & On-Premise Synergy
Protect hybrid environments with consistent policies. Apply the same level of control to your data center, cloud platforms, and SaaS tools.
Cross-Platform Analytics
Leverage insights across ERP, CRM, and productivity tools. Detect risk patterns and abnormal behavior before damage occurs.

Real-Time Visibility Across All Networks
Gain full visibility and control over network health, performance, and threats.

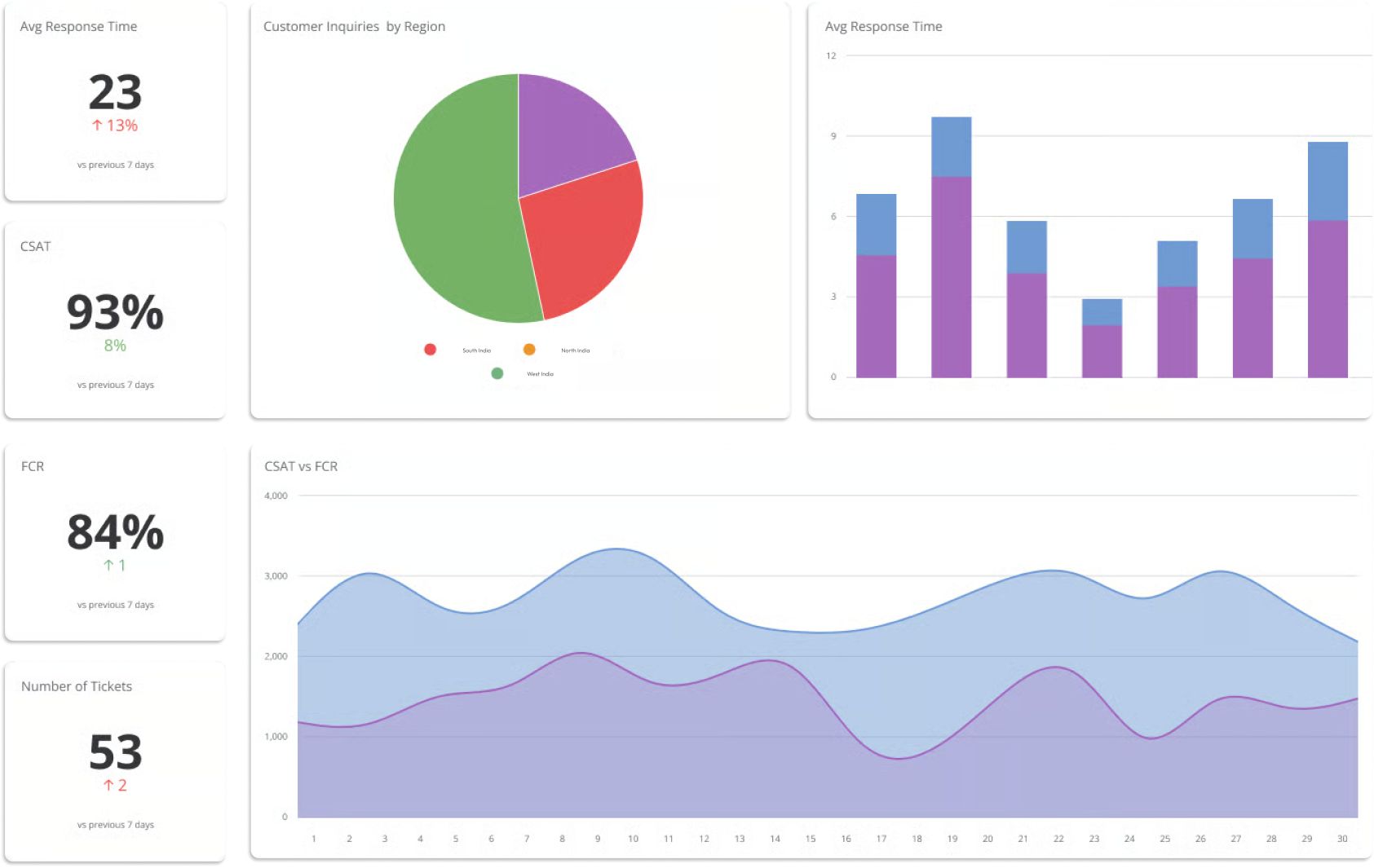
Security Dashboards
Track threat levels, incident history, and patch status in one place. Drive smarter decisions with real-time security intelligence.
Threat Heat Maps
Visualize vulnerable zones, active threats, and attempted breaches across your enterprise. Prioritize mitigation based on risk exposure.
Predictive Risk Analytics
Forecast future threats using AI models. Take preventive action before vulnerabilities turn into exploits.
Let’s get in touch
Your data stays yours. Ablyt ensures 100% privacy — no spam, no sharing.
- Email Us
Our support experts respond within 24 hours on business days.